CEO-Level Guide to Prevent Data Hacking Technologies & Incidents
Security Affairs
JUNE 11, 2021
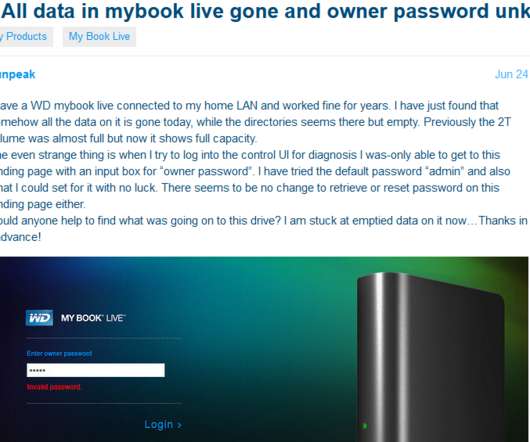
The current era, where all data is digital, the threats of fraud, breach and data sprawl are more of a reality than ever. In these times, organizations not only take a hit because of the breached data and cyber threats, but also are heavily fined under global privacy regulations. These privacy regulations are in place to encourage security operations within organizations to protect their data from malicious intent.



































Let's personalize your content