The Iowa Caucus Tech Meltdown Is a Warning
WIRED Threat Level
FEBRUARY 4, 2020
The Iowa results will come in eventually, thanks to a paper trail. But it underscores just how much can go wrong when you lean on unnecessary, untested tech.

WIRED Threat Level
FEBRUARY 4, 2020
The Iowa results will come in eventually, thanks to a paper trail. But it underscores just how much can go wrong when you lean on unnecessary, untested tech.

Dark Reading
FEBRUARY 4, 2020
For cities, states and towns, paying up is short-sighted and only makes the problem worse.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Threatpost
FEBRUARY 7, 2020
Downloads of files like images may be banned if they use HTTP connections - even if they are available from an HTTPS website.

The Last Watchdog
FEBRUARY 3, 2020
Less than 48 hours after the killing of Iran’s General Qasem Soleimani, the U.S. Department of Homeland Security issued a bulletin calling out Iran’s “robust cyber program,” and cautioning everyone to be prepared for Iran to “conduct operations in the United States.” Related: Cyber warfare enters Golden Age In fact, strategic cyber operations essentially pitting Russia and Iran against the U.S. and Saudi Arabia have been steadily escalating for at least the past decade, with notable spikes
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, VP of Engineering at Betterworks, will explore a practical framework to transform Generative AI pr
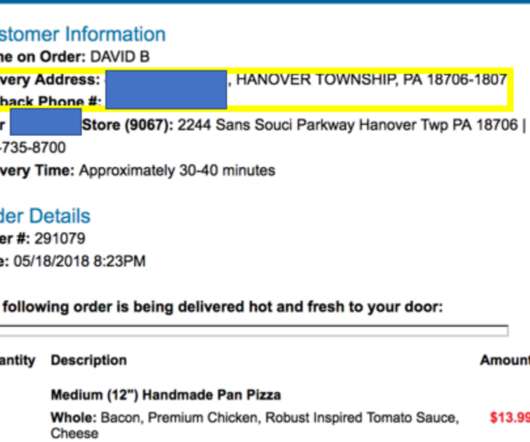
Krebs on Security
FEBRUARY 4, 2020
A Pennsylvania man who operated one of the Internet’s longest-running online attack-for-hire or “booter” services was sentenced to five years probation today. While the young man’s punishment was heavily tempered by his current poor health, the defendant’s dietary choices may have contributed to both his capture and the lenient sentencing: Investigators say the onetime booter boss’s identity became clear after he ordered a bacon and chicken pizza delivered to
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Thales Cloud Protection & Licensing
FEBRUARY 4, 2020
The traditional focus on security has been on breach prevention and threat detection but these can only go so far. For organisations going through digital transformation there needs to be a layered approach to security – complimenting these traditional strategies with data protection.In the evolving digital world of cloud, social and apps, data is now the perimeter.

Adam Levin
FEBRUARY 7, 2020
Online scammers are using the 2020 Oscars to spread malware. A recent study released by Kaspersky Labs uncovered several hacking and phishing campaigns promising their targets free and early access to Best Picture nominees for this year’s Academy Awards. The study found over twenty phishing websites hosting at least 925 malicious files using the movies as bait, requiring would-be victims to either provide personal information (including credit card numbers), or to install adware applications to
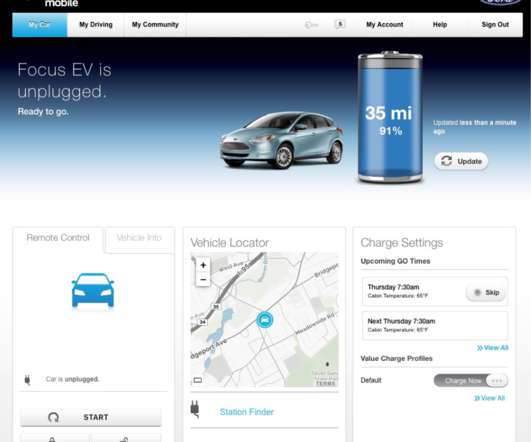
Krebs on Security
FEBRUARY 5, 2020
Many modern vehicles let owners use the Internet or a mobile device to control the car’s locks, track location and performance data, and start the engine. But who exactly owns that control is not always clear when these smart cars are sold or leased anew. Here’s the story of one former electric vehicle owner who discovered he could still gain remote, online access to his old automobile years after his lease ended.

Data Breach Today
FEBRUARY 6, 2020
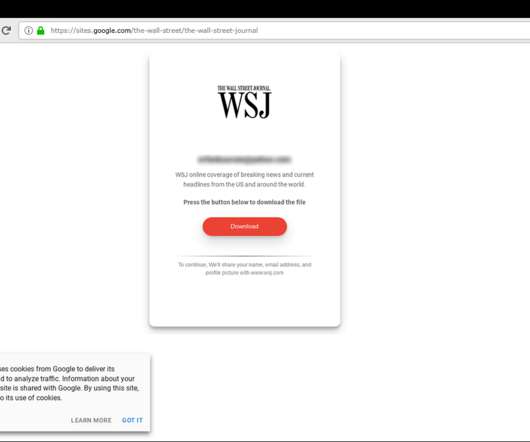
Inquiry Posing Interview Questions Designed to Steal Credentials In a recently discovered phishing campaign, hackers attempted to steal victims' passwords and credentials by posing as a former Wall Street Journal reporter and sending documents with potential interview questions, according to security firm Certfa.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?
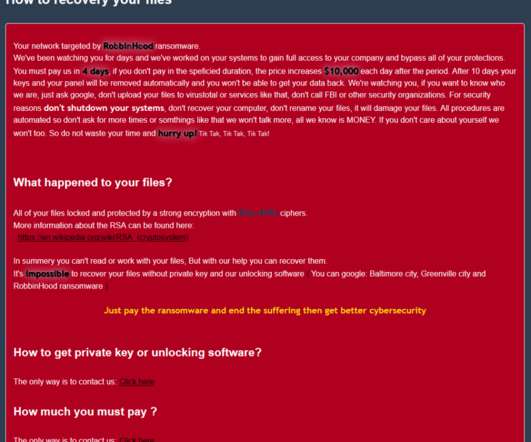
Security Affairs
FEBRUARY 7, 2020
The operators behind the infamous RobbinHood ransomware are exploiting a vulnerable GIGABYTE driver to kill antivirus products. Cybercriminals behind the RobbinHood Ransomware are exploiting a vulnerable GIGABYTE driver to install a malicious and unsigned driver into Windows with the intent of disabling security products. Ransomware operators leverage a custom antivirus killing p ackage that is delivered to workstations to disable security solution before starting encryption.
IT Governance
FEBRUARY 6, 2020
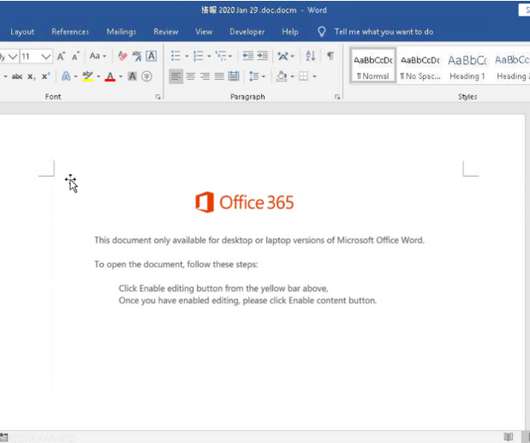
Cyber criminals are exploiting the public’s fear of the Wuhan in a new phishing scam , researchers have learned. Experts at IBM discovered a spate of phishing emails being sent to Japanese citizens, asking them to open an attached Word document supposedly containing details of infections in the country’s main island. The email reads: Department of Health Services.

AIIM
FEBRUARY 6, 2020
Reaching your Digital Transformation goals often requires the addition of new software solutions. But, shopping around for software can be a challenge. How are organizations expected to fully assess the precision of one software system/solution and compare it to another? Are we expected to become experts on each option? In our personal lives, when we shop for something like a new pair of shoes, we try on different brands and sizes to see what fits best for our needs.

Data Breach Today
FEBRUARY 7, 2020
Privacy Rules Remain in Effect Pending Eventual Outcome of UK-EU Negotiations As former U.K. Prime Minister Theresa May famously declared: "Brexit means Brexit." But what Britain's exit from the EU means for the nation's data privacy rules and future EU-U.K. data flows remains to be seen, as the country navigates its post-Brexit transition period.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Security Affairs
FEBRUARY 6, 2020
Check Point experts discovered a high-severity flaw in Philips Hue Smart Light Bulbs that can be exploited to gain entry into a targeted WiFi network. Security experts from Check Point discovered a high-severity flaw ( CVE-2020-6007 ) in Philips Hue Smart Light Bulbs that can be exploited by hackers to gain entry into a targeted WiFi network. Lightbulbs could be remotely controlled through a mobile app or via a digital home assistant, owners could control the light in the environment and even

OpenText Information Management
FEBRUARY 7, 2020
Business continuity can be a challenge when virus breakouts, natural disasters or political upheaval lead to travel bans. While protecting the health of employees and mitigating the risk of spreading the virus are vital, businesses must continue to function and minimize disruption in productivity. For example, the novel coronavirus (2019-nCoV) has recently been declared a … The post Ensuring business continuity during emergencies appeared first on OpenText Blogs.

Thales Cloud Protection & Licensing
FEBRUARY 6, 2020
Artificial intelligence (AI) is becoming increasingly integral to information security. From the multitude of ways AI is used in business to creating smart cities and safeguarding transportation , AI impacts nearly every aspect of our lives. In fact, in its Reinventing Cybersecurity with Artificial Intelligence report , Capgemini found that 61% of respondents said they can no longer detect data breach attempts without the help of AI.

Data Breach Today
FEBRUARY 6, 2020
Sites Fraudulently Offered Government Services for a Fee, Commission Says After winning court approval this week, the Federal Trade Commission shuttered over 200 websites that it says fraudulently claimed to offer government services, such as drivers' license renewals or verification of public benefits, for a fee.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Security Affairs
FEBRUARY 7, 2020
Google addressed a critical vulnerability in its Android OS that affects the Bluetooth subsystem and could be exploited without user interaction. Google has addressed a critical flaw in Android OS that affects the Bluetooth subsystem and could be exploited without user interaction. The vulnerability tracked as CVE-2020-0022 is a remote code execution flaw that could allow attackers to execute code on the device with the elevated privileges of the Bluetooth daemon when the wireless module is acti

AIIM
FEBRUARY 4, 2020
You might think that here at AIIM we’d say everyone is a good candidate for the CIP designation. But, as the architect for the most recent updates to the Certified Information Professional (CIP) certification , a teacher of the CIP prep course, and a CIP pin-wearing member since its release in 2011, I don’t think it’s always a perfect fit. Here at AIIM, the last thing we want is for you to spend your time, money, and effort towards a certification that you won't be happy with in the end.

Troy Hunt
FEBRUARY 6, 2020
I've got audio! Ok, so I cheated a bit in terms of recording back in the home office, but the plugs I need to make the Zoom H6 work the way it should (and yeah, I know I said "Rode" H6 in the vid, sorry!) are on the way and hopefully they'll be all good for next week when I'm in Sydney. I'm talking about that trip in this week's update along with the Chrome 80 changes to SameSite cookies not that its hit, the Adult FriendFinder breach and then recapping on a heap of the week's news in tweets.

Data Breach Today
FEBRUARY 7, 2020
Attorney General Calls for Supporting Huawei's Competitors to Help Boost 5G Security U.S. Attorney General William Barr says the United States and its allies should take a "controlling stake" in Huawei's chief competitors, Findland's Nokia and Sweden's Ericsson, to help make them more viable and improve the security of emerging 5G networks.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
Security Affairs
FEBRUARY 7, 2020
Japanese defense contractors Pasco and Kobe Steel have disclosed security breaches that they have suffered back in 2016 and 2018. Pasco is Japan’s largest geospatial provider and Kobe Steel is one of the major steel manufacturers. Just last week, Japan’s Ministry of Defense announced in addition to Mitsubishi Electric and the NEC defense business division other two unnamed contractors suffered a data breach.

Schneier on Security
FEBRUARY 7, 2020
Ten years ago, I wrote an essay : "Security in 2020." Well, it's finally 2020. I think I did pretty well. Here's what I said back then: There's really no such thing as security in the abstract. Security can only be defined in relation to something else. You're secure from something or against something. In the next 10 years, the traditional definition of IT security -- that it protects you from hackers, criminals, and other bad guys -- will undergo a radical shift.
Jamf
FEBRUARY 3, 2020
This year's global education technology show Bett has a lot of gadgets and flash. But do they actually impact education?

Data Breach Today
FEBRUARY 3, 2020
Lessons Learned from WannaCry and Other Attacks The National Institute of Standards and Technology has unveiled a pair of draft practice guidelines that offer updated advice and best practices on how to protect the confidentiality, integrity and availability of data in light of increasing threats from ransomware and other large-scale cyber events.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

The Guardian Data Protection
FEBRUARY 6, 2020
Ombudsman says ‘greyness’ in metadata definition must be examined as the practice is excluded in legislation Law enforcement agencies are being provided with the web browsing histories of people under investigation using mandatory data retention powers, despite the federal government specifically excluding that practice in the legislation, the commonwealth ombudsman has warned.

IBM Big Data Hub
FEBRUARY 5, 2020
How has the newer data science technology such as Watson Studio, Watson Machine Learning and Watson OpenScale been picked up by the business partner community? I mentioned in our previous blog that I was pleasantly surprised at how many IBM Business Partners have established a Data Science practice. The new data science technology has been very well received by our partner community.

Dark Reading
FEBRUARY 7, 2020
Although radio frequency energy (RF) communications are increasingly essential to modern wireless networking and IoT, the security of RF is notoriously lax.
Let's personalize your content