Will you take the garbage out?
IG Guru
AUGUST 16, 2018
Unmanaged shared files are compared to a shared unmanaged refrigerator. The post Will you take the garbage out? appeared first on IG GURU.

IG Guru
AUGUST 16, 2018
Unmanaged shared files are compared to a shared unmanaged refrigerator. The post Will you take the garbage out? appeared first on IG GURU.

OpenText Information Management
AUGUST 15, 2018
GDPR is finally with us, and within just hours of it becoming law Google and Facebook were hit with privacy complaints that could lead to fines up to $9.3 billion. This is a clear demonstration that the European Union (EU) is very willing to take action and that companies everywhere have to be prepared for GDPR … The post Identity and Access Management is pivotal for GDPR compliance appeared first on OpenText Blogs.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
AUGUST 14, 2018
Attack May Pivot On A Data Breach At 'Unknown Card Issuer' Agency Says The FBI warns that cybercriminals are planning a large-scale operation aimed at emptying ATMs, a type of attack that has caused swift and costly losses for financial institutions. The attack may utilize data from a breach of an unknown card issuer, the FBI says.

Krebs on Security
AUGUST 16, 2018
An entrepreneur and virtual currency investor is suing AT&T for $224 million, claiming the wireless provider was negligent when it failed to prevent thieves from hijacking his mobile account and stealing millions of dollars in cryptocurrencies. Increasingly frequent, high-profile attacks like these are prompting some experts to say the surest way to safeguard one’s online accounts may be to disconnect them from the mobile providers entirely.
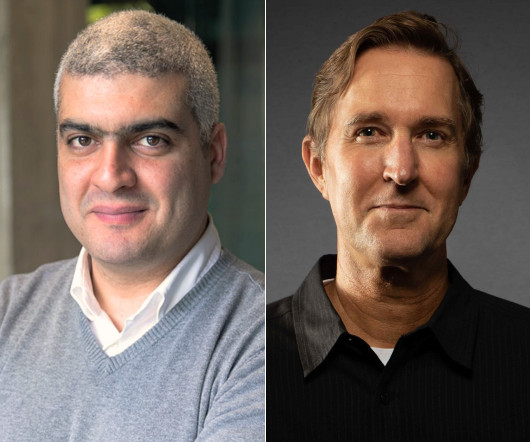
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, VP of Engineering at Betterworks, will explore a practical framework to transform Generative AI pr

The Last Watchdog
AUGUST 15, 2018
In a move to blanket the Internet with encrypted website traffic, Google is moving forward with its insistence that straggling website publishers adopt HTTPS Secure Sockets Layer (SSL). Related: How PKI can secure IoT. Google’s Chrome web browser commands a 60% market share. So the search giant has been leading the push to get 100% of websites to jettison HTTP and replace it with HTTPS.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Data Breach Today
AUGUST 15, 2018
Findings by Watchdog Agency Similar to Problems Previously Cited in Other States Maryland's Medicaid system has "numerous significant" security weaknesses that need to be addressed, according to a federal watchdog agency.

Krebs on Security
AUGUST 12, 2018
The Federal Bureau of Investigation (FBI) is warning banks that cybercriminals are preparing to carry out a highly choreographed, global fraud scheme known as an “ATM cash-out,” in which crooks hack a bank or payment card processor and use cloned cards at cash machines around the world to fraudulently withdraw millions of dollars in just a few hours. “The FBI has obtained unspecified reporting indicating cyber criminals are planning to conduct a global Automated Teller Machine

Thales Cloud Protection & Licensing
AUGUST 17, 2018
In this blog, I will present a new and efficient approach to reconciling security vulnerabilities and FIPS 140 security certifications, led by Thales eSecurity in collaboration with NIST/CMVP and FIPS 140 evaluation laboratories. A quick and efficient patch also needs a quick and efficient certification. To maintain security over a product’s lifetime, it is a best practice for companies to implement a vulnerability management process.

AIIM
AUGUST 16, 2018
It's hard to believe it has been just about 3 months since the General Data Protection Regulation (GDPR) went into effect on May 25th, 2018. This new regulation was designed to strengthen and unify data protection for individuals within the European Union (EU) and came with a strict set of compliance protocols. And, because GDPR also applies to the export of personal data outside the EU, it's applicable to any entity that uses or exchanges this data - so, there are a lot of us all around the wor

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

Data Breach Today
AUGUST 15, 2018
Vulnerability Poses Special Risks For Virtualized Environments The Meltdown and Spectre attacks from earlier this year showed how the quest to make CPUs run faster inadvertently introduced serious security vulnerabilities. Now, researchers have unveiled a new attack called Foreshadow that builds on those findings, affecting millions of Intel processors made over the past five years.

Krebs on Security
AUGUST 17, 2018
On Sunday, Aug. 12, KrebsOnSecurity carried an exclusive : The FBI was warning banks about an imminent “ATM cashout” scheme about to unfold across the globe, thanks to a data breach at an unknown financial institution. On Aug. 14, a bank in India disclosed hackers had broken into its servers, stealing nearly $2 million in fraudulent bank transfers and $11.5 million unauthorized ATM withdrawals from more than two dozen cash machines across multiple countries.

IBM Big Data Hub
AUGUST 13, 2018
Data can be an organization’s most valued asset, providing insights that help strengthen business. Knowing what works and what does not can help you invest more resources in what would work in the future. Learn more about the Watson Knowledge Catalog.

Dark Reading
AUGUST 17, 2018
Simply applying file-based tools and expectations to fileless attacks is a losing strategy. Security teams must also understand the underlying distinctions between the two.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Data Breach Today
AUGUST 14, 2018
Incident at Oklahoma Dept. of Veterans Affairs Spotlights Tough Choices When is it acceptable to allow healthcare workers to use their personal smartphones to access patient records? A recent incident at the Oklahoma Department of Veterans Affairs spotlights the dilemma.

Krebs on Security
AUGUST 15, 2018
Adobe and Microsoft each released security updates for their software on Tuesday. Adobe plugged five security holes in its Flash Player browser plugin. Microsoft pushed 17 updates to fix at least 60 vulnerabilities in Windows and other software, including two “ zero-day ” flaws that attackers were already exploiting before Microsoft issued patches to fix them.

IBM Big Data Hub
AUGUST 16, 2018
IBM Hybrid Cloud Marketing VP Scott Hebner speaks with Big Data and Analytics Hub about the bets he’s placing on the offering to evolve into the company’s first AI platform and emulate WebSphere’s success.

The Guardian Data Protection
AUGUST 15, 2018
The people demanding these new powers have proven that they cannot be trusted with the powers they already have The good news is, the war on maths is postponed, because maths won. The government appears to have given up on its ambition of undermining the global encryption standards that underpin secure communications on the internet. That’s the only good news, because there’s very little positive to be said about the government’s latest lunge for intrusive powers embodied in the Telecommunicatio

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

Data Breach Today
AUGUST 13, 2018
With the rise of the industrial internet of things comes a far broader attack surface in the manufacturing sector. Chris Morales of Vectra outlines findings of a new report on cyberattack trends in the manufacturing sector.

WIRED Threat Level
AUGUST 13, 2018
A new report shows that Google still tracks your location even if you thought you opted out.

IT Governance
AUGUST 17, 2018
IR (incident response) plans are the most effective way of mitigating the damage of data breaches, Ponemon Institute has found. Its 2018 Cost of a Data Breach Study revealed that the average cost of a data breach for organisations without an IR plan was $148 (about £116) per record, which is approximately $14 (about £11) more than those with an IR plan.

The Guardian Data Protection
AUGUST 13, 2018
Proposed laws would also compel Facebook, Apple and Google to assist in decrypting private communications Law enforcement agencies would gain new powers to conduct covert surveillance on electronic devices and compel technology companies to assist in decrypting private communications under proposed legislation. The minister for law enforcement and cyber security, Angus Taylor, released an exposure draft of the bill on Tuesday that would extend obligations to tech giants including Facebook, Apple

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Data Breach Today
AUGUST 13, 2018
Many medical device makers appear to building better cybersecurity into their products, but some manufacturers are still avoiding fixing vulnerabilities in legacy devices that pose potential safety risks, says security researcher Billy Rios, who discusses the latest flaws in some Medtronic cardiac devices.

WIRED Threat Level
AUGUST 16, 2018
A band of activist-entrepreneurs is building a sensor network to warn when and where air strikes will hit—a constant threat under Bashar al-Assad's regime.

IT Governance
AUGUST 11, 2018
Organisations are starting to realise that it’s impossible to prevent every cyber security threat they face, and are turning their attention towards more sophisticated ways of protecting themselves. That typically means becoming cyber resilient – or, in other words, combining cyber defences with business continuity. This enables organisations to not only prevent attacks but also mitigate the disruption, should an incident occur.

Reltio
AUGUST 16, 2018
Ramon Chen, Chief Product Officer, Reltio. On May 25, 2018 GDPR (General Data Protection Regulation) went into effect. The primary objectives of the GDPR are to give control back to their EU citizens and residents over their personal data, to simplify the regulatory environment for international business, and to unify regulations within the European Union.

Advertisement
Start-ups & SMBs launching products quickly must bundle dashboards, reports, & self-service analytics into apps. Customers expect rapid value from your product (time-to-value), data security, and access to advanced capabilities. Traditional Business Intelligence (BI) tools can provide valuable data analysis capabilities, but they have a barrier to entry that can stop small and midsize businesses from capitalizing on them.

Data Breach Today
AUGUST 17, 2018
Leading the latest edition of the ISMG Security Report: Chris Morales of the cybersecurity firm Vectra discusses how the industrial internet of things is changing the nature of industrial espionage and disruption.

WIRED Threat Level
AUGUST 12, 2018
Researchers found they could turn the smart speakers into surveillance devices—if they could get their own attack tool on the same Wi-Fi.

IT Governance
AUGUST 16, 2018
The breadth of applicability of? ISO 27001 ?can make it difficult for organisations to determine how to apply the Standard effectively and economically. As a result, building an? ISMS (information security management system) that meets the requirements of ISO 27001 can be challenging. One solution is to conduct an ISO 27001 gap analysis – a process many organisations consider an important starting point when putting a prioritised plan in place.
Let's personalize your content