How Ransomware Defense is Evolving With Ransomware Attacks
Dark Reading
NOVEMBER 24, 2020
As data exfiltration threats and bigger ransom requests become the norm, security professionals are advancing from the basic "keep good backups" advice.

Dark Reading
NOVEMBER 24, 2020
As data exfiltration threats and bigger ransom requests become the norm, security professionals are advancing from the basic "keep good backups" advice.
Security Affairs
NOVEMBER 23, 2020
Boffins have demonstrated how to steal a Tesla Model X in a few minutes by exploiting vulnerabilities in the car’s keyless entry system. A team of researchers from the Computer Security and Industrial Cryptography (COSIC) group at the KU Leuven University in Belgium has demonstrated how to steal a Tesla Model X in minutes by exploiting vulnerabilities in the car’s keyless entry system.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Threatpost
NOVEMBER 27, 2020
While 2021 will present evolving threats and new challenges, it will also offer new tools and technologies that will we hope shift the balance towards the defense.

IT Governance
NOVEMBER 2, 2020
With 117 publicly reported security incidents, October 2020 is the leakiest month we’ve ever recorded. The good news is that those data breaches and cyber attacks accounted for just 18,407,479 breached records. However, it’s worth noting that, in very few incidents, the number of affected records is revealed – either because the organisation doesn’t know or because it’s not required to disclose that information.
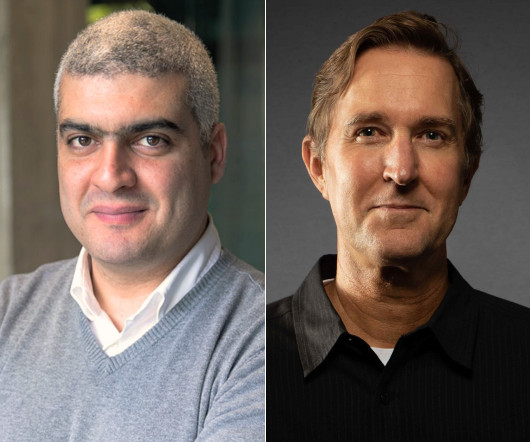
Speaker: Maher Hanafi, VP of Engineering at Betterworks & Tony Karrer, CTO at Aggregage
Executive leaders and board members are pushing their teams to adopt Generative AI to gain a competitive edge, save money, and otherwise take advantage of the promise of this new era of artificial intelligence. There's no question that it is challenging to figure out where to focus and how to advance when it’s a new field that is evolving everyday. 💡 This new webinar featuring Maher Hanafi, VP of Engineering at Betterworks, will explore a practical framework to transform Generative AI pr

Data Breach Today
NOVEMBER 2, 2020
Privacy Regulator in UK Cautions Organizations to Conduct Thorough Due Diligence Hotel giant Marriott has been hit with the second largest privacy fine in British history, after it failed to contain a massive, long-running data breach. But the final fine of $23.8 million was just 20% of the penalty initially proposed by the U.K.'s privacy watchdog, owing in part to COVID-19's ongoing impact.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Krebs on Security
NOVEMBER 21, 2020
Fraudsters redirected email and web traffic destined for several cryptocurrency trading platforms over the past week. The attacks were facilitated by scams targeting employees at GoDaddy , the world’s largest domain name registrar, KrebsOnSecurity has learned. The incident is the latest incursion at GoDaddy that relied on tricking employees into transferring ownership and/or control over targeted domains to fraudsters.
Security Affairs
NOVEMBER 23, 2020
The U.S. FBI is warning private industry partners of a surge in Ragnar Locker ransomware activity following a confirmed attack from April 2020. The U.S. Federal Bureau of Investigation (FBI) issued a flash alert (MU-000140-MW) to warn private industry partners of an increase of the Ragnar Locker ransomware activity following a confirmed attack from April 2020.

Schneier on Security
NOVEMBER 2, 2020
Google’s Project Zero has discovered and published a buffer overflow vulnerability in the Windows Kernel Cryptography Driver. The exploit doesn’t affect the cryptography, but allows attackers to escalate system privileges: Attackers were combining an exploit for it with a separate one targeting a recently fixed flaw in Chrome. The former allowed the latter to escape a security sandbox so the latter could execute code on vulnerable machines.

Troy Hunt
NOVEMBER 25, 2020
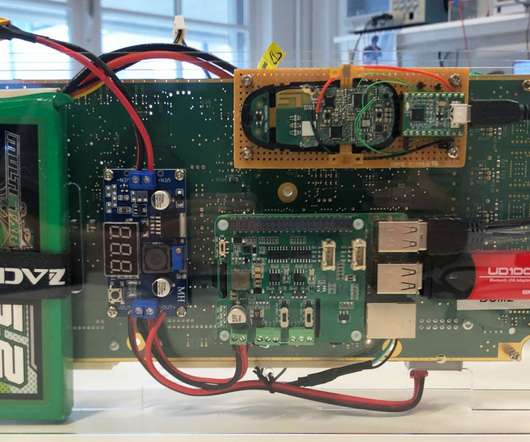
In part 1 of this series, I posited that the IoT landscape is an absolute mess but Home Assistant (HA) does an admirable job of tying it all together. In part 2 , I covered IP addresses and the importance of a decent network to run all this stuff on, followed by Zigbee and the role of low power, low bandwidth devices. I also looked at custom firmware and soldering and why, to my mind, that was a path I didn't need to go down at this time.

Advertisement
Generative AI is upending the way product developers & end-users alike are interacting with data. Despite the potential of AI, many are left with questions about the future of product development: How will AI impact my business and contribute to its success? What can product managers and developers expect in the future with the widespread adoption of AI?

Data Breach Today
NOVEMBER 28, 2020
Agency Says Hackers Can Use a Known Bug for Further Exploitation CISA is warning about a possible password leak that could affect vulnerable Fortinet VPNs and lead to further exploitation. The latest agency notice comes just days after hackers began publishing what they claim are leaked passwords on underground forums, according to researchers.

IT Governance
NOVEMBER 23, 2020
Amid the mad dash for bargains and inevitable stories of shop-floor brawls, Black Friday brings with it a spike in cyber security threats, as cyber criminals take advantage of people desperate for bargains. In this blog, we look at some of the scams you should look out for and what you can do to protect yourself. Why Black Friday is primetime for cyber crime.
Krebs on Security
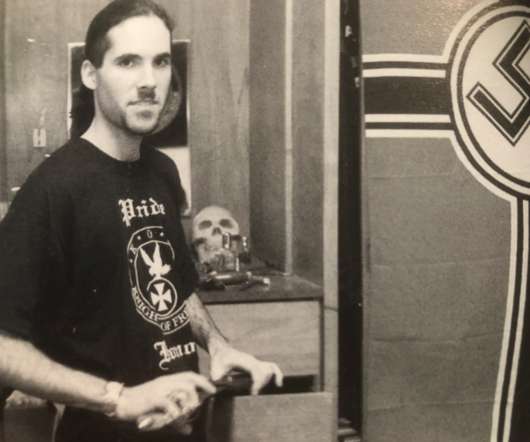
NOVEMBER 8, 2020
The body of a man found shot inside a burned out vehicle in Canada three years ago has been identified as that of Davis Wolfgang Hawke , a prolific spammer and neo-Nazi who led a failed anti-government march on Washington, D.C. in 1999, according to news reports. Homicide detectives said they originally thought the man found June 14, 2017 in a torched SUV on a logging road in Squamish, British Columbia was a local rock climber known to others in the area as a politically progressive vegan named
Security Affairs
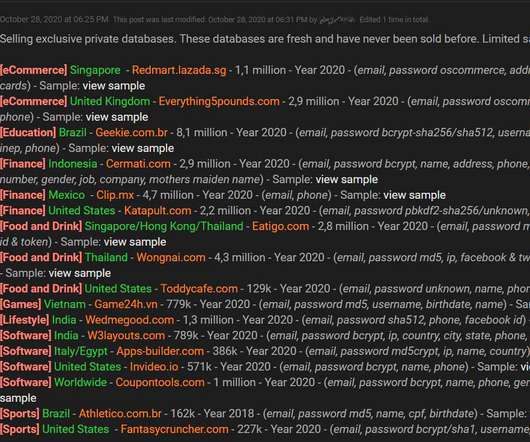
NOVEMBER 1, 2020
A threat actor is offering for sale account databases containing an aggregate total of 34 million user records stolen from 17 companies. A data breach broker is selling account databases containing a total of 34 million user records stolen from 17 companies. The threat actor is advertising the stolen data since October 28 on a hacker forum. Source Bleeping Computer.
Advertisement
Many organizations today are unlocking the power of their data by using graph databases to feed downstream analytics, enahance visualizations, and more. Yet, when different graph nodes represent the same entity, graphs get messy. Watch this essential video with Senzing CEO Jeff Jonas on how adding entity resolution to a graph database condenses network graphs to improve analytics and save your analysts time.

Schneier on Security
NOVEMBER 24, 2020
Wired has a detailed story about the ransomware attack on a Dusseldorf hospital, the one that resulted in an ambulance being redirected to a more distant hospital and the patient dying. The police wanted to prosecute the ransomware attackers for negligent homicide, but the details were more complicated: After a detailed investigation involving consultations with medical professionals, an autopsy, and a minute-by-minute breakdown of events, Hartmann believes that the severity of the victim’s medi

Troy Hunt
NOVEMBER 26, 2020
This is the fifth and final part of the IoT unravelled blog series. Part 1 was all about what a mess the IoT landscape is, but then there's Home Assistant to unify it all. In part 2 I delved into networking bits and pieces, namely IP addresses, my Ubiquiti UniFi gear and Zigbee. Part 3 was all about security and how that's all a bit of a mess too, particularly as it relates to firmware patching and device isolation on networks.

Data Breach Today
NOVEMBER 12, 2020
WildWorks Data Breach Shows Danger of Sharing Sensitive Keys Over Chat Chat and collaboration software tools such as Slack are critical for software development teams. But a data breach experienced by Utah-based software developer WildWorks illustrates why developers should think twice before sharing sensitive database keys over chat.

WIRED Threat Level
NOVEMBER 13, 2020
Last fall, a hacker gave Glenn Greenwald a trove of damning messages between Brazil’s leaders. Some suspected the Russians. The truth was far less boring.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.
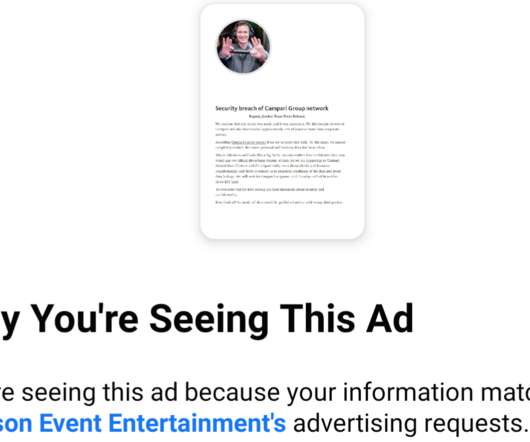
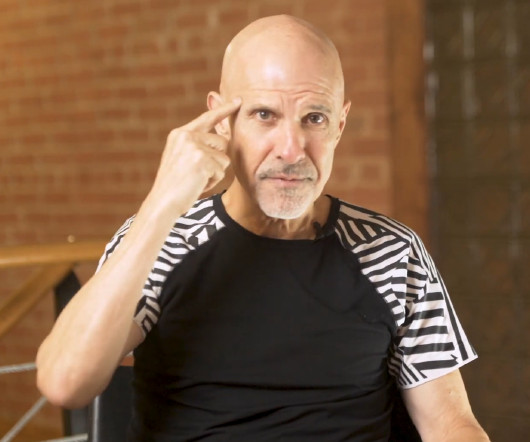
Krebs on Security
NOVEMBER 10, 2020
It’s bad enough that many ransomware gangs now have blogs where they publish data stolen from companies that refuse to make an extortion payment. Now, one crime group has started using hacked Facebook accounts to run ads publicly pressuring their ransomware victims into paying up. On the evening of Monday, Nov. 9, an ad campaign apparently taken out by the Ragnar Locker Team began appearing on Facebook.
Security Affairs
NOVEMBER 10, 2020
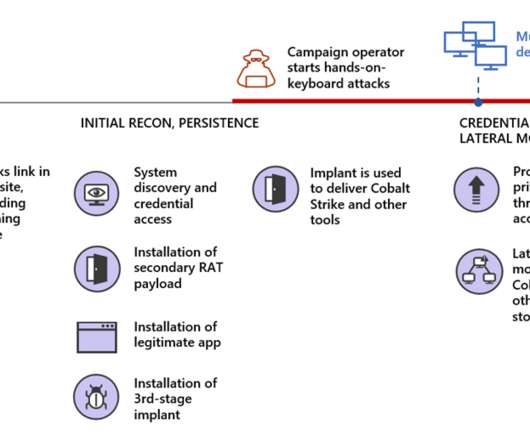
Ransomware operators use fake Microsoft Teams updates to deploy Cobalt Strike and compromise the target networks. Ransomware operators are using malicious fake Microsoft Teams updates to deliver backdoors that lead the installation of the Cobalt Strike post-exploitation tool and compromise the target network. The ongoing COVID-19 pandemic is forcing a growing number of organizations and businesses in using videoconferencing solutions, and threat actors are attempting to exploit this scenario.

Schneier on Security
NOVEMBER 4, 2020
Accuracy isn’t great, but that it can be done at all is impressive. Murtuza Jadiwala, a computer science professor heading the research project, said his team was able to identify the contents of texts by examining body movement of the participants. Specifically, they focused on the movement of their shoulders and arms to extrapolate the actions of their fingers as they typed.
Troy Hunt
NOVEMBER 2, 2020
I've had this blog post in draft for quite some time now, adding little bits to it as the opportunity presented itself. In a essence, it boils down to this: people expressing their displeasure when I post about a topic they're not interested in then deciding to have a whinge that my timeline isn't tailored to their expectation of the things they'd like me to talk about.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.
Data Breach Today
NOVEMBER 10, 2020
Investigators Find Encryption, Monitoring, Logging and Whitelisting Failures Inadequate database and privileged account monitoring, incomplete multi-factor authentication and insufficient use of encryption: Britain's privacy regulator has cited a raft of failures that contributed to the four-year breach of the Starwood guest reservation system discovered by Marriott in 2018.
John Battelle's Searchblog
NOVEMBER 30, 2020
Why “information equity” matters. An idea has been tugging at me for months now, one I’ve spent countless hours discussing and debating with leaders in marketing, media, and journalism. And as I often do, I’m turning to writing to see if I can push it into more concrete form. I’m literally thinking out loud here, but I won’t bury the lede: I believe it’s time for all major corporations – not just the companies that pushed for the #StopHateForProfit

Krebs on Security
NOVEMBER 4, 2020
Companies hit by ransomware often face a dual threat: Even if they avoid paying the ransom and can restore things from scratch, about half the time the attackers also threaten to release sensitive stolen data unless the victim pays for a promise to have the data deleted. Leaving aside the notion that victims might have any real expectation the attackers will actually destroy the stolen data, new research suggests a fair number of victims who do pay up may see some or all of the stolen data publi
Security Affairs
NOVEMBER 1, 2020
Japan’s Nuclear Regulation Authority (NRA) issued a warning of temporary suspension of its email systems, likely caused by a cyber attack. The Japan’s Nuclear Regulation Authority (NRA) temporarily suspended its email systems, the interruption is likely caused by a cyber attack. The agency published a warning on its website, it is asking people to contact it via phone or fax because it is unable to receive emails from the outside world. “From 17:00 on October 27, 2nd year of Reiwa, sending

Speaker: Nicholas Zeisler, CX Strategist & Fractional CXO
The first step in a successful Customer Experience endeavor (or for that matter, any business proposition) is to find out what’s wrong. If you can’t identify it, you can’t fix it! 💡 That’s where the Voice of the Customer (VoC) comes in. Today, far too many brands do VoC simply because that’s what they think they’re supposed to do; that’s what all their competitors do.

Schneier on Security
NOVEMBER 10, 2020
Over at Lawfare: “ 2020 Is An Election Security Success Story (So Far).” What’s more, the voting itself was remarkably smooth. It was only a few months ago that professionals and analysts who monitor election administration were alarmed at how badly unprepared the country was for voting during a pandemic. Some of the primaries were disasters.

Troy Hunt
NOVEMBER 25, 2020
The first few parts of this series have all been somewhat technical in nature; part 1 was how much of a mess the IoT ecosystem is and how Home Assistant aims to unify it all, part 2 got into the networking layer with both Wi-Fi and Zigbee and in part 3 , I delved into security. Now let's tackle something really tricky - humans. I love the idea of automating stuff in the home, but I love the idea of a usable home even more.
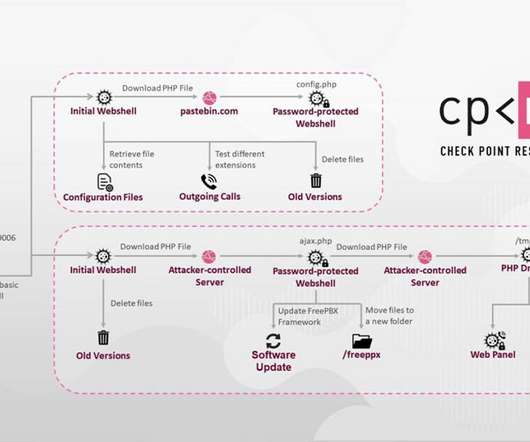
Data Breach Today
NOVEMBER 9, 2020
Attackers Exploit a Vulnerability in Asterisk VoIP PBX Servers Check Point Research has uncovered a large and likely profitable business model that involves hackers attacking and gaining control of certain VoIP services, which enables them to make phone calls through a company's compromised system.
Let's personalize your content